Risk management in software engineering is defined as the process of identifying, analysing, ranking, and treating risks that may threaten the success of a software engineering project. It is a set of actions and strategies that are taken to reduce the possibility of risks and their impacts by the achievement of the laid down project goals and objectives. The main aim of risk management is to contain the amount of risk and improve the quality of decision-making because it considers threats and turns them into strategic concerns before they become critical problems.
Importance of Risk Management
- Project Success: Risk management helps recognise risks and deal with them before they become serious, which may help keep projects on schedule, on budget, and to the desired standard.
- Resource Optimization: Managing risks enables the successful use of some resources, scrap avoidance, and direction of attention to critical project aspects.
- Stakeholder Confidence: Advance risk management can be effective. It can increase the stakeholders’ confidence, as it emphasises delivering a reliable product.
- Adaptability: Risk management helps teams better prepare for any changes in scenarios and inconvenient situations that may arise, keeping the project on track and steady ground.
- Cost Control: Identification and management of risks to avoid negative consequences that could lead to overtime and thus cost more than what the project was designed to spend.
Overview of Risk Management Process
The risk management process in software engineering typically involves the following steps.
- Risk Identification: The first is identifying risks that might harm the project. This involves using brainstorming, checklists, historical data analysis, and SWOT analysis to identify risks.
- Risk Analysis and Evaluation: After identifying risks, they are assessed to understand their potential consequences and the chances of their occurrence. This step can be either qualitative, where assessment tools such as the Probability and Impact Matrix are applied or quantitative, where Monte Carlo Simulation and Decision Tree Analysis are used.
- Risk Prioritization: The results from the risk evaluation are then ranked against the likelihood of occurrence and their impact on the business. To summarise, high-probability risks represent crucial risks likely to occur and deserve prompt attention.
- Risk Response Planning: In this step, the management strategy entails taking measures to contain the above risks.
- Avoidance: Changing the project schedule in such a way that it will minimise the risk.
- Mitigation: Measures that can be taken to minimise the prospect or magnitude of the threat.
- Transfer: This creates a twofold risk division between risk avoidance and risk shifting, typical of insurance and outsourcing.
- Acceptance: Recognising that an adverse event may happen and drawing up a plan to mitigate if it does occur.
- Risk Monitoring and Control: Risk management must be monitored across the project life cycle since risk is never far from the picture. This means carrying out risk analysis periodically, risk review, and risk audits to achieve an updated risk management plan to cover all emerging risks.
- Risk Communication: To manage risks in an organisation, there must be good communication between the different departments. It maintains openness in handling risks, the planned measures to prevent them from materialising, and the changes in their status.
Types of Risks in Software Engineering:
1. Technical Risks
Technological risks are related to the selection, use, and methodology of technology that shall be used in software development. Such risks may be associated with the technology selection, the application’s intricacy, and performance issues.
Technology Changes
The software industry is highly volatile, and new solutions can often appear. Implementing modern technologies can sometimes prove beneficial, but it is also risky. Integration problems can occur with new or developing technology, compatibility problems with some developing technology, and training problems can occur to accommodate some new or developing technology. When the programmer changes the current programming language or framework mid-project, the programmer will most likely encounter new and unfamiliar bugs and may take time to develop solutions.
Software Complexity
Software systems being used and functional means that systems become more extensive and complex, thus increasing difficulty in designing and implementing the systems. High complexity may also render the software tricky to comprehend, test, and alter, and defects may increase.
Performance Issues
Operational risks relate to the software’s capacity to deliver the requisite performance characteristics, including reaction time, quantity constitutive throughput, and scalability. Negativity impacts the users, suboptimal and unstable system functioning, and the inability to provide necessary processing to high loads.
2. Project Management Risks
It is a circumstance within a project resulting from activities carried out about its planning, execution, and control. When it comes to project risks, there is one thing that should be understood: these threats can affect the schedule of the project, cause consumption of resources, and increase expenses.
Schedule Slippage
The following factors may result in extending project time horizons: new requirements, risks and problems, and the ineffectiveness of one’s management. There is always a danger that, due to such slippages, a project may run out of time and cost more than planned, or worse, stakeholders may lose their confidence in project managers.
Resource Shortages
Resource scarcity can be defined as the unavailability of human, financial, or other resources needed for a given project. A lack of resources can slow down the processes within the project, combine its quality, and put pressure on the project team members.
Budget Overruns
Cost control issues can be summarised as a situation whereby the project’s total cost is beyond the planned or expected budget because of wrong estimation, changes in the project scope, or the discovery of new activities that require funding. Going over the cost can put the project’s financial sustainability at risk and result in clients’ or users’ discontent.
3. Organizational Risks
Project risks relate to the operational and organisational aspects of the venture that implements the software project. These risks can occur because of activities such as conflicts, changes in management, and restructurings.
Stakeholder Conflicts
Criticisms can also emanate from conflicts or differences of opinion from the various stakeholders on goals, objectives, or specifications. These disputes may result in time extension for the specific project, high costs, and the absence of a supposed single vision.
Management Changes
Fluctuation at the leadership or core management levels can interfere with the project’s continuity and disturb various decision-making propositions. When management changes, there is always a shift in organisational focus and direction, objective changes, and sometimes a lack of project experience.
Organisational Restructuring
Transforming refers to significant modifications that may occur in the formal structure, business practices, or strategies within the company and may affect the project. A common consequence of restructuring is resource redistribution, a shift in the scale of projects, and the possible deterioration of working relations.
4. External Risks
External risks affect the projects external to the organisation and are not easily influenced by the project team. It may be around changes in regulations that govern the company’s operations, fluctuations in the market, and disasters such as floods, among others.
Regulatory Changes
New policies, either in Government, standards, codes of practice, or any other, may impact the requirements or the constraints placed on the project. That requires changes in the software, new compliance activities, and costs.
Market Fluctuations
Fluctuations in the market indices, for instance, depression or changes in the market about the project feasibility and success rate. That is why many factors can influence the project process, including, for example, changes in the market that can cause fluctuations in funding for a particular project, as well as changes in its priority or the scope of work to be done.
Natural Disasters
Project activities may be affected by Earthquakes, floods, or hurricanes. Catastrophes may occur and affect schedules and assets, and more money may be required to restore and maintain the business.
Risk Identification
Risk identification in software engineering forms one of the steps in risk management processes. It entails the identification of risks that are likely to hurt the project in question. Thus, risk identification allows the project teams to tackle problems properly before they worsen.
Techniques for Identifying Risks
- Brainstorming: Risk identification is the imaginative process where an organisation generates ideas concerning potential threats. Redefining the goals and objectives would help the project succeed. Promoting the cross-talk and exchange of ideas. A technique of outlining all possible risks without the necessity of making an instant appraisal and assessment of each. Arranging the risks that have been identified for further classification to be done. Brainstorming assists in amplifying available and unique knowledge and ideas to find as many risks as possible that may not be apparent at first.
- Delphi Technique: The Delphi technique is carried out by independent and unbiased experts who do not disclose their identities and give possible risks. Picking people with different experiences and codified information in the field. Surveys should be conducted in several cycles, during which respondents are entitled to mention threats and make recommendations.
- Checklists are preset lists of typical hazards that can impact software projects. They rely on historical facts and the standard practices in the business world. Reflecting on all the categories raised when checking on a detailed risk list.
- Historical Data Analysis: Historical Data Analysis presupposes the investigation of past performed work, which may embrace risks that have taken place. Original data generated from the project, including risk logs and project post-mortem. Evaluating the occurrences, consequences, and possible sources of previous risk. Finding specificities and regularities may point to risks in the current project. Historical Data Analysis uses the information gained from previous events, and it helps organisations avoid specific dangers.
- SWOT Analysis: SWOT Analysis evaluates the company’s internal capabilities and lack of them to identify the opportunities and threats in its business environment that affect the project.
Tools for Risk Identification
- Risk Breakdown Structure (RBS): The Risk Breakdown Structure (RBS) refers to a tree-structured list of risks classified according to types. Evaluating priorities of the risks and establishing the basic risk classes (technical, project, organisational).
- Cause and Effect Diagrams: Fishbone or Ishikawa Diagrams relate potential causes to their consequences and help make the relationship between them easily understandable.
- Risk Registers: Based on the current literature, a Risk Register can be described as a documented record of identified risks and their characteristics and responses toward those risks.
Risk Analysis and Evaluation
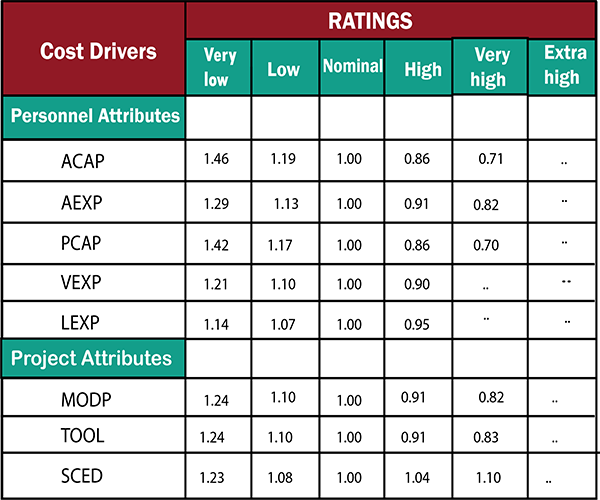
Qualitative Risk Analysis
1. Probability and Impact Matrix
A probability and impact matrix, another elementary but effective tool, ranks risks about probability and impact. The matrix generally comprises a chart with risks being plotted in it.
- Probability: The chance that the risk will happen. This is usually rated on a scale (low, medium, high).
- Impact: The possible consequences of facing the actual probability of the risk. This is also rated on the scale (insignificant, moderate, and significant).
2. Risk Urgency Assessment
Risk: Risk Urgency Assessment is concerned with determining the risk’s potential to impact the project and the time the risk could occur. It assists in identifying threats that require urgent attention and thus prioritising them.
Quantitative Risk Analysis
1. Monte Carlo Simulation
Monte Carlo Simulation is a method of prediction that utilises quantitative analysis of risk impacts in a project. When one sets different inputs and conducts several simulations, it gives a probability view of risks.
- Define Variables: Acknowledge and describe the drivers that characterise a project (time, cost, quality, resources, etc. ).
- Assign Probability Distributions: Following this, one can assign probability distributions to these variables by using records or relying on the heuristics.
- Run Simulations: The method is to apply software, which means running thousands of simulations with inputs varied randomly based on their distribution is possible.
2. Decision Tree Analysis
It was discovered that Decision Tree Analysis is a graphical technique for making decisions in conditions of risk. It entails creating a chart of various decision trees, their consequences, and the likelihood of the outcome and the effect.
- Define Decision Points: Determine critical decisions that can be made throughout the project.
- Map Decision Paths: I will create branches for each possible decision and all corresponding outcomes.
- Assign Probabilities: Conclusively, estimating the probability of each possible outcome is possible.
- Calculate Expected Values: Calculate the expected worth for each decision course by multiplying the likelihoods with the extent of the outcome.
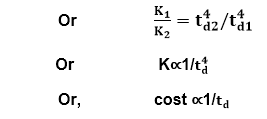
3. Sensitivity Analysis
Sensitivity Analysis analyses variations in these project characteristics on the result. It determines the height of vulnerability and the exposure level of each variable influencing project risk most heavily.
- Identify Variables: Key project variables, such as cost and time spent on the project.
- Change Variables: Make systematic alterations only to one fair condition at a time while there are no other affairs.
- Measure Impact: Analyse the impact of each of those changes on the results achieved in the framework of projects.
- Analyze Sensitivity: Determine which variables influence the project risk to the highest degree.
Risk Prioritization:
Therefore, Risk prioritisation forms part of risk management strategies that help the teams tackle the risks with the highest probability first.
Risk Ranking Methods
1. Risk Exposure Formula
Risk Exposure (RE) is computed mathematically with the help of the Risk Exposure formula, which gives a quantitative measure of risk exposure. It is arrived at by the product of the likelihood of the risk event and the consequence of the risk event on the project.
Risk Exposure (RE) = Probability of occurrence*Impact
- Probability of Occurrence: This is the approximate probability that a specific risk will occur, and most often, they are presented in percentage.
- Impact: The result indicates the approximate possible loss or harm in the event of the risk, which is sometimes described in terms of cost, time, or quality.
2. Failure Mode and Effects Analysis or FMEA
Failure Mode and Effects Analysis (FMEA) is a step-by-step process for failure identification in a system along with its consequences.
- Identify Failure Modes: Enumerate all the scenarios by which a process, product, or system can go wrong.
- Determine Effects: To evaluate each failure mode, the following should be answered:
- Assign Severity Ratings: Categorise the failure modes’ impact on a severity scale.
- Assign Occurrence Ratings: Approximate the occurrence of the described failure mode on a scale as well.
- Assign Detection Ratings: Rate the effectiveness of preventing each failure mode from occurring before it results in a problem on the same scale.
- Calculate Risk Priority Number (RPN): The severity ranking, occurrence frequency, and detection efficiency are multiplied to arrive at the RPN for each failure mode.
RPN = Severity*Occurrence*Detection
Prioritisation Techniques
Pareto Analysis
Pareto Analysis, which follows the Pareto principle (80/ 20 rule), enables one to determine the few significant risks that can cause the most probable issues.
- List Risks: It is also essential to list all possible risks.
- Quantify Impact: Evaluate the effect of each risk. Usually, it’s presented in the form of cost, time, or how frequently the event can occur.
- Sort Risks: Sort possible risks in decreasing order due to the impact estimation.
- Cumulative Impact: Determine the added-up effect of the risks that have been identified.
- Identify Top Risks: Learn which risks will have the most significant impacts and determine that, typically, these are the first 20% of risks that create approximately 80% of the potential losses.
Risk Score Calculation
Risk Score Calculation provides several risk scores depending on specified factors such as probability and consequence.
- Define Criteria: Set out guidelines to ascertain risks, usually using risk probability and severity parameters.
- Assign Scores: Assign a scale of 1 to 5 to each risk for each criterion you have come up with.
- Calculate Risk Score: Average/Total the score of each risk to arrive at its overall risk score.
Risk Response Planning:
Risk response planning is the step that involves identifying the measures that can increase the likelihood of achieving the project’s aims as well as matching the threats that may hinder its success. It requires assessing what risks must be managed and what responses must be made to them.
Strategies for Risk Response
- Avoidance: This requires alteration of the project plan either to avoid the risk or the effects of risk. It can consist of changing requirements, better communication channels, or acquiring more information to avoid the risk. For example, a particular project can have methods of data backup and recovery to reduce the chances of data loss.
- Mitigation: Mitigation seeks to minimise the probability of a risk or the severity of its effect. This can include practices that will reduce the impact of the risk factor or its occurrence probability. For instance, a team could incorporate other systems and prop up strict maintenance schedules to avoid such system failure.
- Transfer: Risk transfer is one of the risk response strategies wherein the consequences of a risk are moved to the third party. This does not remove the risk but ensures that another firm bears the consequences. These include buying insurance, hiring third parties to provide some of the project’s features, or operating under a contract with conditions that shift risk.
- Acceptance: It means understanding the volatility of the situation and choosing to live with it should anything go wrong. This approach is often used where the cost of elimination or reduction is higher than the resulting consequence. For instance, a team may agree to live with minor faults in secondary product functionality that is not a priority since the cost of squashing them is prohibitive.
Risk Monitoring and Control:
Risk monitoring and control are some of the critical parts of risk management systems within software engineering. They ensure that the identified risks are monitored, assessed, and managed not only at the initial and then at the end of the SDLC but throughout the entire process. It’s essential in sustaining project objectives, quality, and time considerations due to its distinct features that differ from the traditional approach.
1. Continuous Risk Monitoring
Risk assessment focuses on regularly observing and evaluating possible risks that may influence a particular software project. This is a forward-thinking approach aimed at ensuring that all risks likely to occur within an organisation are dealt with well from the word go.
- Risk Tracking: Periodically amending the risk register by updating it with the status of the identified risks.
- Environmental Scanning: Keeping track of alterations that may occur within the sphere of the project that are unfavourable and potentially pose new risks to the work being done.
- Trend Analysis: The evaluation of the risks to identify potential problems that may occur in the future and adapt them to the existing ones.
2. Risk Audits
Risk audits are proactive activities of enterprises aimed at assessing the organisation and efficiency of risk management within the scope of a specific project.
- Compliance Checks: Ensuring that the risk management activities comply with the standards and policies.
- Effectiveness Assessment: Assessing the effectiveness of the risk responses and the effectiveness of the implemented risk management strategies.
- Improvement Recommendations: The need to develop recommendations and areas in processes to work on is well identified.
3. Status Meetings and Reviews
This form of communication should also include regular status meetings and reviews concerning risk management responsibilities. These statuary meetings enable the provision of information and ensure all the stakeholders are informed.
- Progress Reports: Informing on changes in risks’ status and on the efficiency of actions aimed at their mitigation.
- Stakeholder Involvement: Informing the project’s essential stakeholders about risks and their effects on the project.
- Decision Making: Decision-making support based on the current risk data and their analysis.
4. Risk Reassessment
Risk review is the process of carrying out the risk register check at least once in a while to add new notes or decrees about this risk in the project environment. This makes it possible for that risk management plan to be current and efficient.
- Periodic Reviews: Carry out periodic risk register updates to arrive at new risks and re-evaluate old risks.
5. Performance Metrics and KPIs
Performance indicators are applied to evaluate risk management efficiency, and Key performance indicators are a particular type of performance indicator. It gives quantitative data that one can use to mark the effectiveness in dealing with risks.
- Risk Exposure: Estimating the threat or the potential harm of identified risks to the project.
- Risk Mitigation Success Rate: Measuring the raw incidence of the successfully mitigated risks.
- Time to Mitigate Risks: Measuring the average days it takes to address and respond to the risks.
- Cost of Risk Management: Measuring the return on investment on the implemented risk management activities.
Tools and Techniques for Risk Management:
Risk Management Software
Specifically, Risk Management Software is created to introduce, evaluate, and control risks at any phase of the software development.
- RiskWatch: Some key risk assessment features are real-time data with robust risk management tools and features incorporated in the tool series.
- Active Risk Manager (ARM): Leads the integration of risk management processes into the project management process integrations.
- Palisade’s DecisionTools Suite has risk assessment and decision-making capabilities such as Monte Carlo simulation and risk probability.
Tools for Project Management with Risk Management Aspects
Today, most PMSs have a built-in risk management function that factors this process into the overall PM framework.
- Microsoft Project: Has integrated functions for risk management integrated within comprehensive project planning tools.
- JIRA: Out of all the available tools, JIRA, commonly used in agile development, is equipped with risk tracking as one of the features of managing projects and issues.
- Trello: This is based on boards and cards for handling tasks and risks with extensible modules for final enhanced risk management.
Collaborative Tools for Risk Tracking
Information technologies improve the communication process between the team members and increase understanding of the existing threats and appropriate measures.
- Slack: There are channels and threads for team discussions and possible integrations with the risk management tools.
- Confluence: An open-access platform that allows the team to record the risks, report changes, and work together on the measures needed to address the risks.
- Microsoft Teams: It enhances communication and cooperation by inserting options for document sharing and project management.