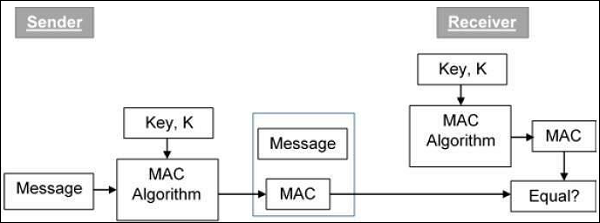
MAC (Message Authentication Code) algorithm is a symmetric key cryptographic technique to provide message authentication. For establishing MAC process, the sender and receiver share a symmetric key K.
Essentially, a MAC is an encrypted checksum generated on the underlying message that is sent along with a message to ensure message authentication.
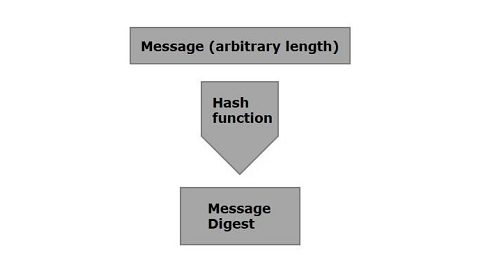
The process of using MAC for authentication is depicted in the following illustration −
In Java the Mac class of the javax.crypto package provides the functionality of message authentication code. Follow the steps given below to create message authentication code using this class.
Step 1: Create a KeyGenerator object
The KeyGenerator class provides getInstance() method which accepts a String variable representing the required key-generating algorithm and returns a KeyGenerator object that generates secret keys.
Create KeyGenerator object using the getInstance() method as shown below.
//Creating a KeyGenerator object
KeyGenerator keyGen = KeyGenerator.getInstance("DES");
Step 2: Create SecureRandom object
The SecureRandom class of the java.Security package provides a strong random number generator which is used to generate random numbers in Java. Instantiate this class as shown below.
//Creating a SecureRandom object
SecureRandom secRandom = new SecureRandom();
Learn Java in-depth with real-world projects through our Java certification course. Enroll and become a certified expert to boost your career.
Step 3: Initialize the KeyGenerator
The KeyGenerator class provides a method named init() this method accepts the SecureRandom object and initializes the current KeyGenerator.
Initialize the KeyGenerator object created in the previous step using this method.
//Initializing the KeyGenerator
keyGen.init(secRandom);
Step 4: Generate key
Generate key using generateKey() method of the KeyGenerator class as shown below.
//Creating/Generating a key
Key key = keyGen.generateKey();
Step 5: Initialize the Mac object
The init() method of the Mac class accepts an Key object and initializes the current Mac object using the given key.
//Initializing the Mac object
mac.init(key);
Step 6: Finish the mac operation
The doFinal() method of the Mac class is used to finish the Mac operation. Pass the required data in the form of byte array to this method and finsh the operation as shown below.
//Computing the Mac
String msg = new String("Hi how are you");
byte[] bytes = msg.getBytes();
byte[] macResult = mac.doFinal(bytes);
Example
The following example demonstrates the generation of Message Authentication Code (MAC) using JCA. Here, we take a simple message “Hi how are you” and, generate a Mac for that message.
import java.security.Key;
import java.security.SecureRandom;
import javax.crypto.KeyGenerator;
import javax.crypto.Mac;
public class MacSample {
public static void main(String args[]) throws Exception{
//Creating a KeyGenerator object
KeyGenerator keyGen = KeyGenerator.getInstance("DES");
//Creating a SecureRandom object
SecureRandom secRandom = new SecureRandom();
//Initializing the KeyGenerator
keyGen.init(secRandom);
//Creating/Generating a key
Key key = keyGen.generateKey();
//Creating a Mac object
Mac mac = Mac.getInstance("HmacSHA256");
//Initializing the Mac object
mac.init(key);
//Computing the Mac
String msg = new String("Hi how are you");
byte[] bytes = msg.getBytes();
byte[] macResult = mac.doFinal(bytes);
System.out.println("Mac result:");
System.out.println(new String(macResult));
}
}Output
The above program will generate the following output −
Mac result:
HÖ„^ǃÎ_Utbh…?š_üzØSSÜh_ž_œa0ŽV?